SSL Configuration in Tomcat using Keystore
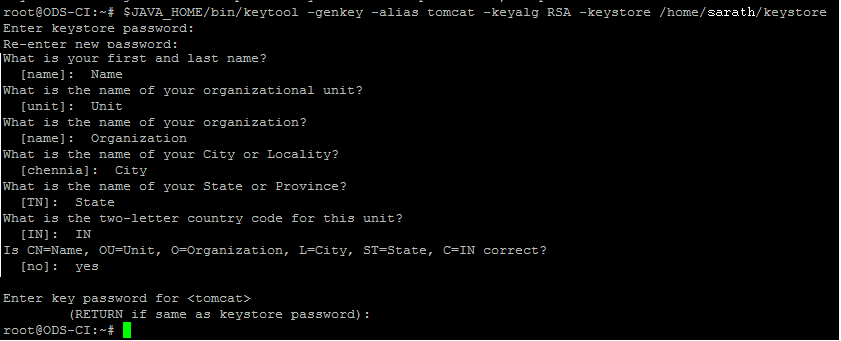
Tomcat currently operates with JKS, PKCS11 or PKCS12 format keystores. To create a new keystore from scratch, containing a single self-signed Certificate, execute the following from a terminal command line:
$JAVA_HOME/bin/keytool -genkey -alias tomcat -keyalg RSA
The above command will create a new file named ".keystore" in the home directory of the user under which you run it. To specify a different location, add "-keystore" followed by pathname to your keystore file at the end of the command. The sample command is as follows:
$JAVA_HOME/bin/keytool -genkey -alias tomcat -keyalg RSA -keystore <<path to your keystore file>>
After executing the above command, you will be prompted for password. Default password used by tomcat is "changeit". You can also specify the password of your own. Once the password has been specified, you will be prompted for the general information about this certificate, such as company, contact name, and so on. This information will be displayed to users who attempt to access a secure page in your application, so make sure that the information provided here matches what they will expect.
Finally, you will be prompted to enter password, which should be the same password as used for the keystore password itself. Currently, the keytool prompt will tell you that pressing the ENTER key does this for you automatically.
A sample screenshot is given below:
If everything was successful, you are done and now have a keystore file with a Certificate that can be used by your server.
Once the password is set, the specified password should be kept in server.xml configuration file.
<-- Define a SSL Coyote HTTP/1.1 Connector on port 8443 -->
<!--
<Connector
port="8443" maxThreads="200"
scheme="https" secure="true" SSLEnabled="true"
keystoreFile="${user.home}/.keystore" keystorePass="changeit"
clientAuth="false" sslProtocol="TLS"/>
-->
Restart your tomcat server and you are done!

Comments
Post a Comment